Old Pitfalls, New Wounds: Analysis of Stolen Authorized Malicious Contracts
It is recommended that users frequently check whether there are any abnormal authorization situations and cancel them in time.
Written by: Zero, Lisa
background
Recently, the SlowMist security team has been exposed to several coin theft incidents caused by authorization. These incidents are the simplest coin theft caused by Approve authorization. The key point is that the victim accidentally clicked Approve authorization a long time ago. Fortunately, the characteristics of blockchain–passing geese leave traces, and clues can always be found in a large amount of on-chain data.
Stolen case analysis
According to the information provided by the victim, the stolen transactions were as follows:
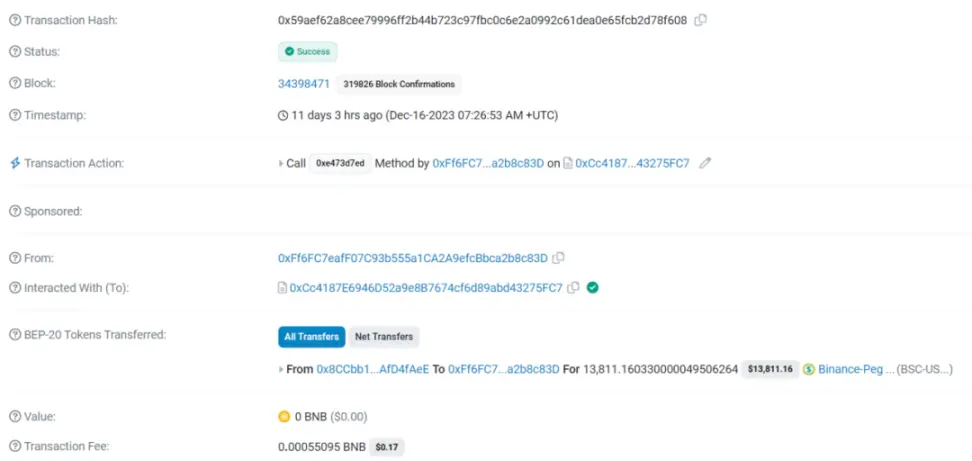
()
At a glance, it can only be seen that the victim address 0x8CCb was stolen by the hacker address 0xFf6F with 13,811 USDT stolen.
This transaction is neither an off-chain permit/permit2 signature method nor any authorization method with other contract vulnerabilities, nor is it a create2 method.
After we eliminated these common methods, we found that this transaction was actually the simplest token theft caused by Approve authorization, and it was the fuse that was laid a long time ago.
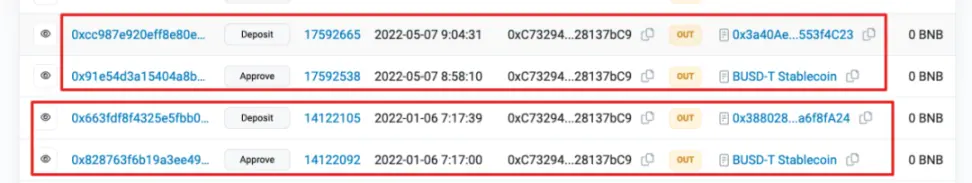
By analyzing the previous on-chain transaction records, it was discovered that the key point of the theft is that the victim had authorized a contract address (0x3880285800a89AB3C4338bf455acdA3da6f8fA24) more than two years ago. The authorization record is as follows:
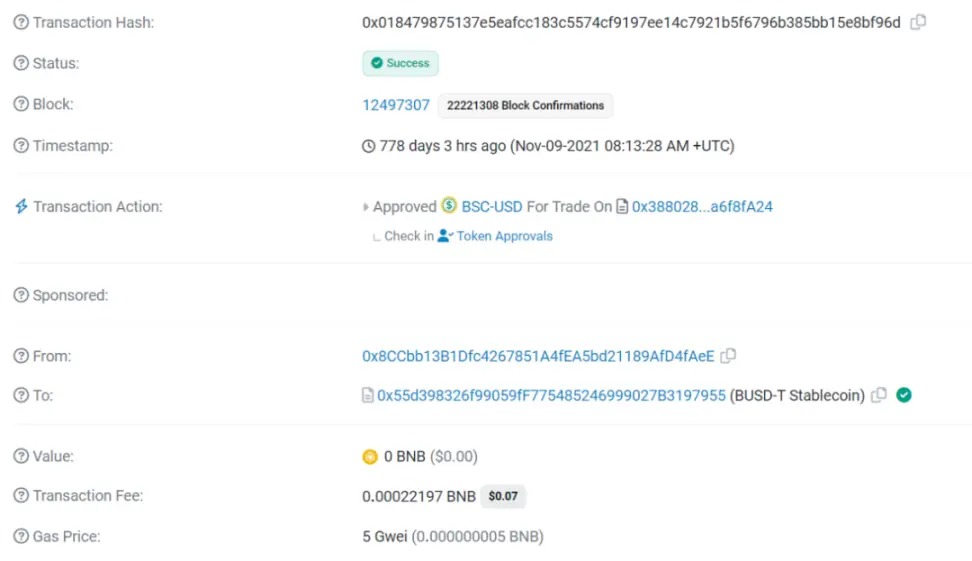
()
The timeline of authorized transactions and stolen transfers is listed below, with a gap of up to 767 days:
- November 9, 2021, 08:13:28 - Malicious authorization of transactions to malicious contract addresses;
- December 16, 2023, 07:26:53 - USDT-BEP20 was transferred without authorization.
How were the funds stolen after being authorized to the malicious contract address? Let’s take a closer look at the details.
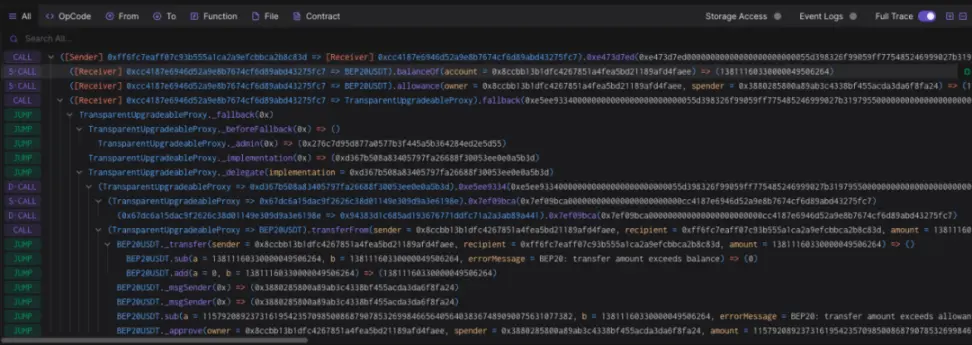
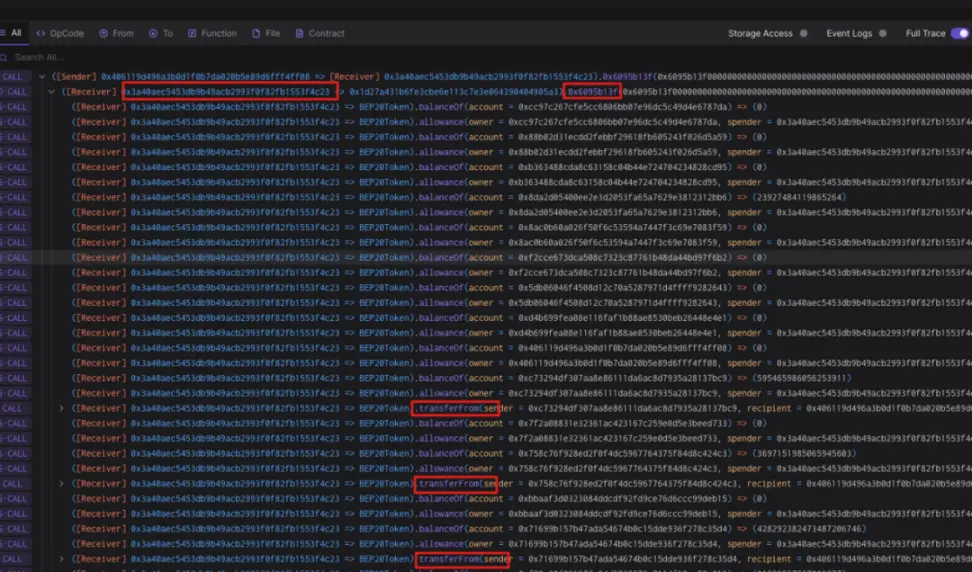
()
In this transaction, the following steps occur:
- By calling the 0xe473d7ed method of the 0xcc4187 contract address, check the balance of the stolen address and the Allowance authorized to the malicious contract;
- Call the 0xe5ee9334 method of the Proxy contract 0xd367b5 of the malicious contract (TransparentUpgradeableProxy in the figure):
- Verify the Role permissions of the 0xcc4187 contract address;
- The malicious contract calls the transferFrom function of USDT-BEP20 as the msg sender, thereby transferring the Token assets authorized to the malicious contract to the hacker’s profit address 0xFf6F.
MistTrack Analysis
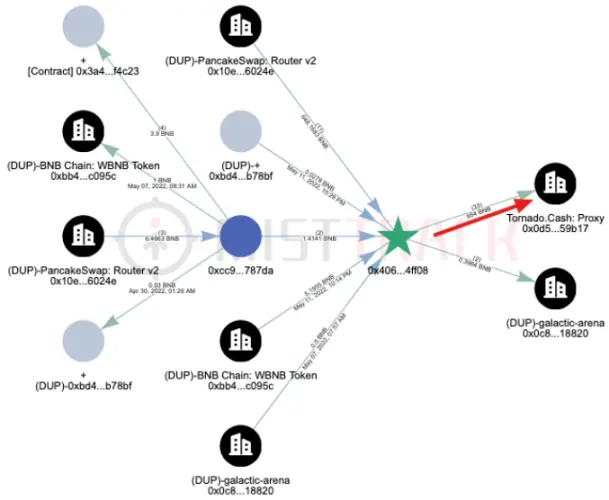
According to MistTrack analysis, the hacker address (0xFf6FC7eafF07C93b555a1CA2A9efcBbca2b8c83D) has currently made approximately $200,000 in profits, including a variety of tokens.
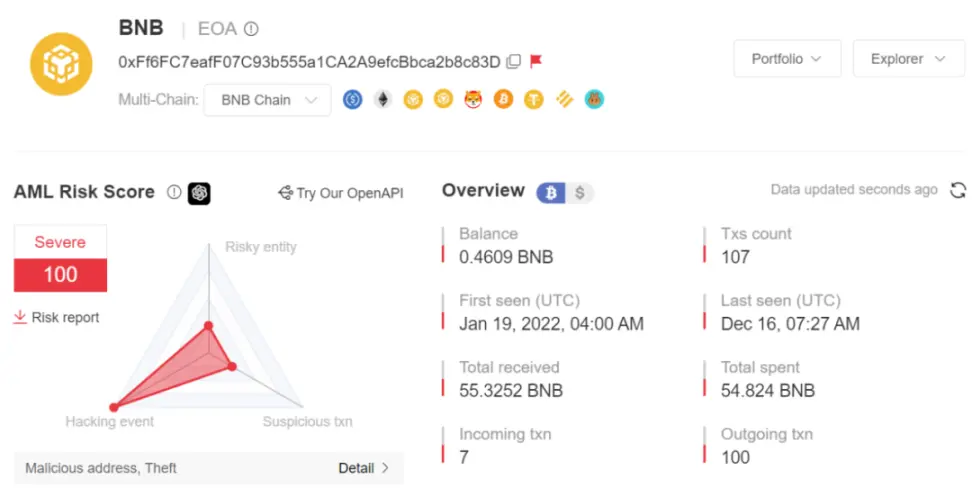
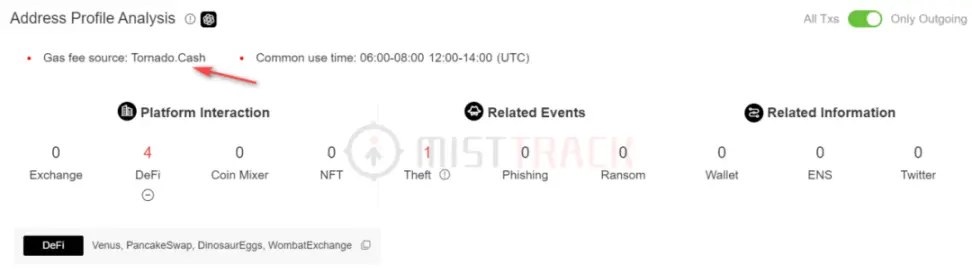
The hacker’s initial funds came from 0.098 BNB transferred from Tornado Cash, and he used Venus, PancakeSwap, DinosaurEggs, and WombatExchange:
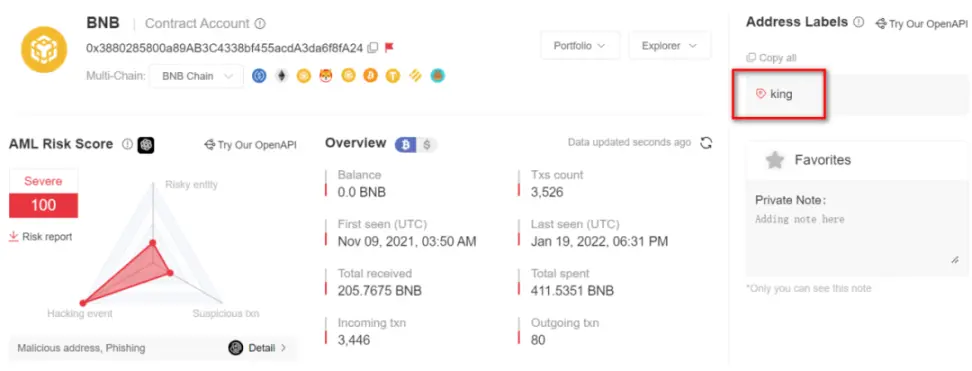
Next, we analyze the malicious contract address (0x3880285800a89AB3C4338bf455acdA3da6f8fA24):
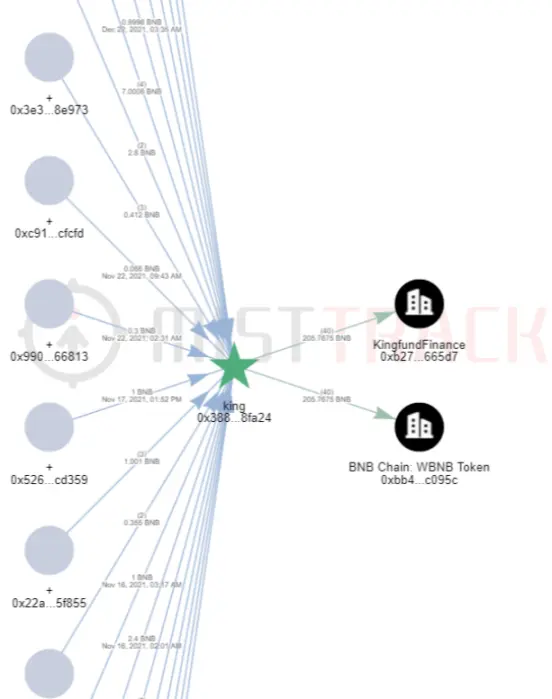
We found that this malicious contract was marked as King in MistTrack, which means that this contract address is the contract address of the original project King. This contract address also interacts with Kingfund Finance. King and Kingfund Finance should be the same project:
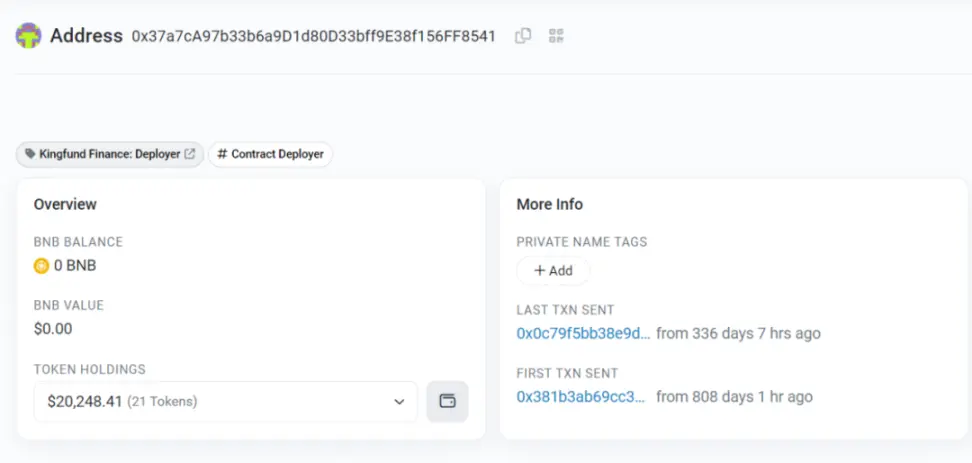
Let’s look at the creator address of the malicious contract address (0x37a7cA97b33b6a9D1d80D33bff9E38f156FF8541), which is marked as Kingfund Finance: Deployer.
When we searched for information about this project, we found that it was actually a RugPull project. On January 19, 2022, Kingfund Finance took away more than 300 WBNB (approximately US$141,000) and closed its official website and official Twitter. In other words, users who have not deauthorized the malicious contract are still being stolen. The SlowMist security team recommends users to cancel the authorization of the malicious contract in a timely manner.
Dune Data Analysis
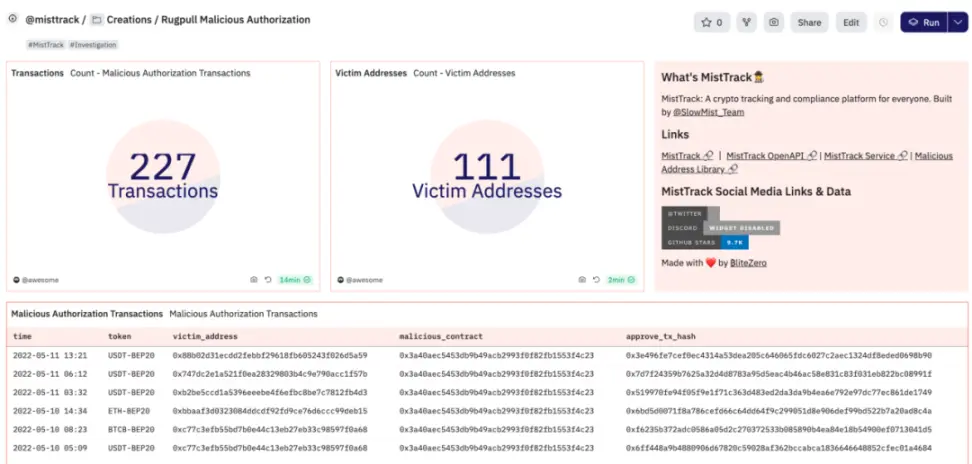
()
Based on the characteristics summarized above and with the help of Dune analysis, we also found that another user authorized the above-mentioned malicious contract address (0x3880285800a89AB3C4338bf455acdA3da6f8fA24) in January 2022, and then authorized another RugPull malicious contract address in May ( 0x3a40AeC5453dB9b49ACb2993F0F82FB1553f4C23).
The creator of this malicious contract (0x406119D496a3b0D1F0B7DA020B5e89d6FFf4Ff08) has transferred most of the profit-making funds to Tornado Cash.
The relevant address has been blocked by MistTrack.
Summarize
This article mainly introduces a case in which subsequent funds were continuously stolen due to authorization to the RugPull project in the early years, and expands the Dune data set based on relevant characteristics. Phishing is pervasive and you can be caught accidentally. The SlowMist security team recommends that users frequently check their authorization status. You can use RevokeCash, ScamSniffer, Rabby and other tools to check. If you find any abnormal authorization, please cancel it in time.