GoPlus Emergency Alert: High-Risk Vulnerability in the EngageLab SDK, Potential Exposure of Private Keys for 30 Million Crypto Wallets

GoPlus, a blockchain security platform, issued an emergency alert on April 10, stating that the EngageLab SDK—used broadly for Android push notifications—has a serious security vulnerability. The issue affects more than 50 million Android users, including about 30 million cryptocurrency wallet users. Attackers can deploy malicious code disguised as legitimate applications on the victim devices to steal cryptocurrency wallet private keys and login credentials.
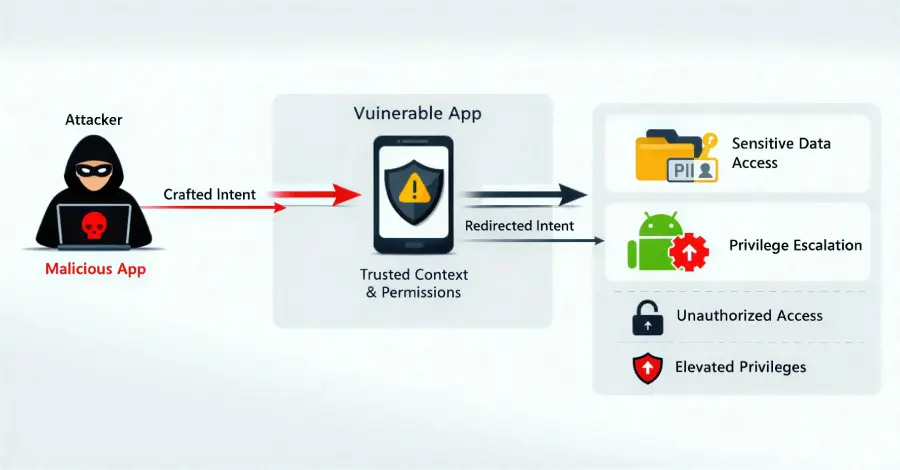
Vulnerability technical principle: a cross-application attack chain executed silently
 (Source: GoPlus)
(Source: GoPlus)
The core flaw in this vulnerability is that the EngageLab SDK does not perform sufficient source validation when handling Android’s Intent communication mechanism. Intent is a legitimate mechanism for passing commands between Android applications, but the EngageLab SDK’s implementation allows commands from unauthorized sources to bypass the normal validation process, triggering the target application to perform sensitive operations.
Full attack chain in three steps
Malicious app implantation: The attacker disguises malicious code as a legitimate App, tricking victims into installing it on the same Android device.
Malicious Intent injection: The malicious app sends a carefully crafted malicious Intent to a cryptocurrency wallet or financial application on the same device that has already integrated the EngageLab SDK.
Privilege-escalation operation execution: After the target app receives the Intent, it executes unauthorized actions without the user’s knowledge, including stealing wallet private keys, login credentials, and other sensitive data.
The greatest danger of this attack chain lies in its stealthiness: victims do not need to take any active action. As long as the device contains both a malicious application and an EngageLab SDK application with the vulnerable version, the attack can be completed in the background.
Scale of impact: irreversible asset-loss risk for crypto users
As a widely deployed building block for push notifications, the EngageLab SDK has been integrated into thousands of Android applications, bringing the scope of this vulnerability to a scale of 50 million devices. Among them, approximately 30 million are cryptocurrency wallet users.
Once a cryptocurrency wallet private key is exposed, attackers can fully take control of the victim’s on-chain assets. Additionally, the irreversible nature of blockchain transactions means losses of this type are nearly impossible to recover, making the risk far greater than ordinary application data breach incidents.
Emergency response measures: an immediate action checklist for developers and users
Segmented security recommendations
- Application developers and vendors
· Immediately check whether your product integrates the EngageLab SDK, and confirm whether the current version is below 4.5.5
· Upgrade to the EngageLab SDK 4.5.5 or later official patched version (please refer to EngageLab’s official documentation)
· Re-release the updated version, and notify users to complete the update as soon as possible
- General Android users
· Immediately go to Google Play to update all apps, prioritizing cryptocurrency wallet and financial apps
· Stay alert to apps downloaded from unknown sources or non-official channels; delete them immediately if necessary
· If you suspect the private key has been leaked, you should immediately create a new wallet on a secure device, transfer assets, and permanently disable the old address
Frequently asked questions
What is the EngageLab SDK, and why is it widely integrated into cryptocurrency wallets?
The EngageLab SDK is a third-party software package that provides Android push notification functionality. Because it is convenient to deploy, it is adopted by many applications. Push notifications are a standard feature in nearly all mobile applications, which is why the EngageLab SDK is also widely present in cryptocurrency wallets and financial applications—leading to this vulnerability affecting 50 million users.
How can I confirm whether my device is affected by this vulnerability?
If your Android device has a cryptocurrency wallet or financial app installed, and it has not yet been updated to the latest version, there is a risk of being affected. It is recommended to update all apps immediately in the Google Play store. Developers can verify whether they use an EngageLab SDK version lower than 4.5.5 by checking the SDK version number within the app.
If a private key has already been leaked, what should be done urgently?
Immediately create a brand-new wallet address on an uncompromised secure device, transfer all assets from the original wallet to the new address, and permanently disable the old address. At the same time, change login passwords for all relevant platforms and enable two-factor authentication for the account to reduce the risk of further compromise.